 News Corporation (News Corp) has disclosed more information about the 2022 cyberattack against the major publishing conglomerate. News Corp revealed that the cybercriminals had access to its systems two years ago, starting in Feb. 2020.
News Corporation (News Corp) has disclosed more information about the 2022 cyberattack against the major publishing conglomerate. News Corp revealed that the cybercriminals had access to its systems two years ago, starting in Feb. 2020.
News Corp recently sent notification letters to affected employees. These laid out the most recent information on the data breach. The breach affected workers at the company’s publications, The New York Post and The Wall Street Journal, and its UK news operations.
The Dates of the Breach and Affected Information
Hackers accessed News Corp data from Feb. 2020 to Jan. 2022. News Corp discovered the
breach on Jan. 20, 2022, and took immediate action.
The breach allowed attackers access to emails and business documents from limited personnel. Although the attackers accessed personal details, this doesn't seem to be their goal. There are no reports of identity fraud from the breach.
How News Corp Reacted
News Corp immediately hired cybersecurity firm Mandiant to investigate the breach. The
company also contained the activity.
News Corp has also arranged 24 months of Experian credit monitoring and identity protection. This comes at no cost to the employees. It covers identity theft insurance, credit monitoring, and identity restoration.
Final Thoughts
This type of data breach is becoming common. If it can affect a company as large as News Corp, then business owners should take it seriously. Be proactive with prevention and monitoring to catch potential breaches or malware early. This is essential to protecting you and your customers. It will also help maintain the reputation of your business. Even small business owners should take steps to protect themselves and their clients from data breaches.
One way to protect your data is to call Integrated Technology Systems. We specialize in data security.
Password Mask Attacks
 Having a password for online accounts is not enough protection. Hackers and cybercriminals have found a way to crack passwords and hijack emails, bank accounts, social media pages, and other digital real estate. Through password mass attacks, cyber threat actors no longer have to spend a long time trying to guess your online credentials.
Having a password for online accounts is not enough protection. Hackers and cybercriminals have found a way to crack passwords and hijack emails, bank accounts, social media pages, and other digital real estate. Through password mass attacks, cyber threat actors no longer have to spend a long time trying to guess your online credentials.
Understanding a Password Mass Attack
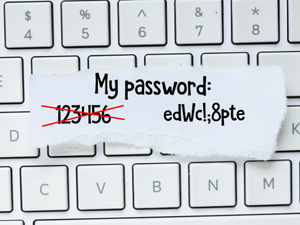
A password mask attack is a technique cybercriminals use to crack passwords. While a conventional brute-force attack tries to guess your password by entering every possible letter, number, and symbol combination, a mask attack is more targeted and takes less time. It is also more systematic.
With a mask attack, cybercriminals check passwords for a specific pattern. Knowing this pattern allows them to skip character combinations that are not necessary.
Threat actors will use information about your password creation behavior, including your composition patterns. They will then start cracking a subset of your password's format or entire length.
How Does a Password Mask Attack Work?
Websites and online apps do not store their users' passwords verbatim. Instead, they use a process called hashing. Hashing uses an encryption algorithm to turn passwords and other data into a string of letters and numbers.
Hashing improves the security of your password. So, if attackers hack a website, they won't be able to access your password as is. Instead, they will get the encrypted "hash" that the algorithm had created.
If cybercriminals get a hold of password hashes from a site, they can start a password mask attack. They will put the character combinations into a hashing function and wait until they get valid hits or until it creates a hash that matches yours. These cybercriminals can calculate hashes for common words and often-used combinations.
Cybercriminals don't crack each password within the data set they obtained from a website. They only need to crack enough passwords to get an initial foothold on the website and go deeper into their attack.
How to Prevent Password Mask Attacks
It is important for businesses with websites to take steps to prevent password mask attacks. Their websites must encourage customers or individual users to create strong passwords. Strong passwords contain a combination of uppercase and lowercase letters, numbers, and special characters. With stronger passwords, cybercriminals would find it hard to guess the patterns and calculate hashes.
Businesses and organizations with websites can also use password managers. These tools help prevent network security threats by storing and managing users' credentials. Moreover, they address password security issues like weak passwords and password reuse.
The Bottom Line: Protect Business Sites and Customers From Mask Attacks
Password mask attacks on a business website put customer data at risk. Once cybercriminals crack passwords, they can also extract personal data and use them to access bank accounts. Or they can launch smaller attacks targeted at individuals. Customers will lose confidence in a business if this happens. A mask attack can also disrupt business operations. As such, businesses should encourage their users to create strong passwords. They should also use password managers to protect passwords and customer credentials.
Integrated Technology Systems is here to help. We can train your employees on how to be on high alert for cyber attacks. Call us today to we how w can assist your business.
Integrated Technology Systems
6 East 45th Street, Suite 400
New York, NY 10017
212-750-5420
https://www.itsnyc.com



